Perfect stack: A step-by-step guide to layering bracelets — Covet & Acquire

Stacking Your Bracelets – How To Do It Right

The Ultimate Guide to Creating the Perfect Bracelet Stack

TAU Threat Advisory: Microsoft Exchange Servers Targeted wit - vulnerability database

IT threat evolution in Q2 2022. Non-mobile statistics - vulnerability database
RATs and stealers rush through “Heaven's Gate” with new load - vulnerability database

Qualcomm Careers, Engineering Jobs and More

Remote Code Execution (RCE) - vulnerability database

Perfect stack: A step-by-step guide to layering bracelets — Covet & Acquire

What's happening in the world of crimeware: Emotet, DarkGate - vulnerability database

CVE-2021-40444 PoC - Malicious docx generator to exploit CVE - vulnerability database

Informational: Impact of Spring Vulnerabilities CVE-2022-229 - vulnerability database
PHP-Rake-IDF/idf.json at master · scrivna/PHP-Rake-IDF · GitHub
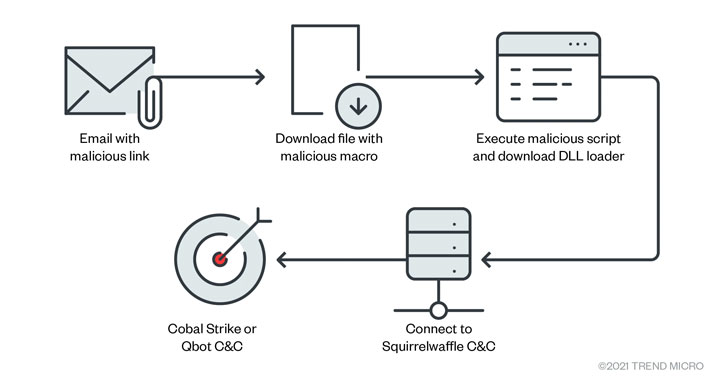
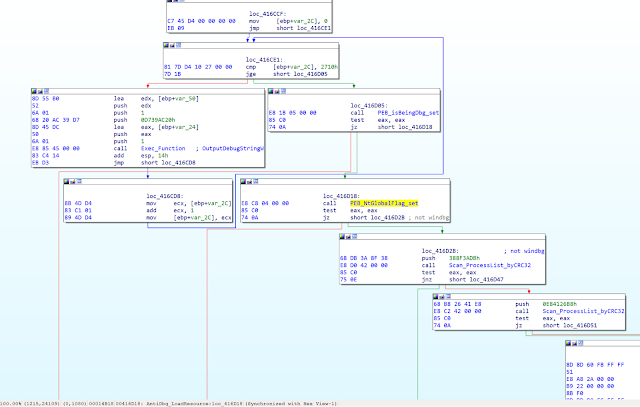
Hackers Exploiting ProxyLogon and ProxyShell Flaws in Spam C - vulnerability database
Perfect stack: A step-by-step guide to layering bracelets — Covet & Acquire
- Best Price $ 96.99. Good quality and value when compared to hfhealthcare.org similar items.
- Seller - 746+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Louis Vuitton Monogram Empreinte Felicie Pochette (SHF-fOsLlf) – LuxeDH
Buy It Now 4d 14h -

Louis Vuitton LV Instinct Pendant
Buy It Now 2d 5h -

Neverfull leather clutch bag Louis Vuitton Brown in Leather - 31758842
Buy It Now 21d 11h -

Louis Vuitton Vintage - Epi Saint Jacques Long Strap GM Bag - Red
Buy It Now 3d 9h -

Hermès Garden Party Handbag
Buy It Now 3d 20h -

M43895 Louis Vuitton 2018 Men Messenger PM-Monogram Glaze
Buy It Now 28d 21h -

Louis Vuitton Monogram Gradient T-Shirt – S&Co Clothing
Buy It Now 14d 22h -
Kylie Jenner
Buy It Now 15d 21h -

Antique Beaded Purse/victorian Purse/floral Beaded Bag/antique
Buy It Now 9d 20h -

Buy Charles & Keith Curved Tote Bag In Blue
Buy It Now 11d 15h -

ailouis Expandable Extra Large Wheeled Travel Duffel Luggage Bag 36 inch Black
Buy It Now 13d 22h -

Keychain Bear Liquid Floating Quicksand Cute Keychains Bag Charm Wristlet Bracelet Key Ring For Women Girl
Buy It Now 4d 19h -

Los Angeles Lakers Kobe Bryant 1996 Home Authentic Jersey By Mitchell & Ness - Light Gold - Mens
Buy It Now 21d 19h -

Louis Vuitton Rose Ballerine Quilted Calfskin Small New Wave Camera Bag Gold Hardware, 2018 Available For Immediate Sale At Sotheby's
Buy It Now 10d 11h -

Mäntel und Jacken - Kollektion für Herren
Buy It Now 13d 6h -
Bottega Veneta Loop Intrecciato Leather Crossbody Bag - Bergdorf Goodman
Buy It Now 15d 16h -

Rec. plaza senayan LV Alma BB damier ebene 2022
Buy It Now 3d 21h -

M&M's Milk Chocolate Holiday Candy, 18oz Bag, Chocolate Candy
Buy It Now 13d 6h -
M&M's Crunchy Mint Chocolate Candy Sharing Size Bag, 8 Oz.
Buy It Now 22d 21h -

Purse Organizer Insert,Felt Bag Organizer with NEW Detachable Zipper cover, fits LV, Goyard St Lious, Tote and handbag shaper – ztujo
Buy It Now 3d 6h -

Men's Keychains & Lanyards - Luxury Designer Key Holders
Buy It Now 26d 12h -

Motorcraft Mercon LV ATF 0.946 L : : Business, Industry
Buy It Now 12d 6h -

Supreme Louis Vuitton/Supreme Baseball Gloves ❤ liked on Polyvore
Buy It Now 21d 21h -

Gold Metal LV Louise Hoop Earrings
Buy It Now 24d 21h



