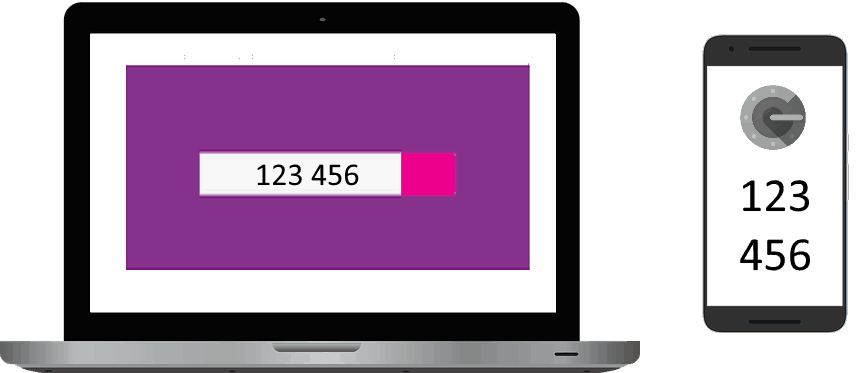
Authentification Guide — Two authenticators
$ 1000.00 Buy It Nowor Best Offer, FREE Shipping, 30-Day Returns
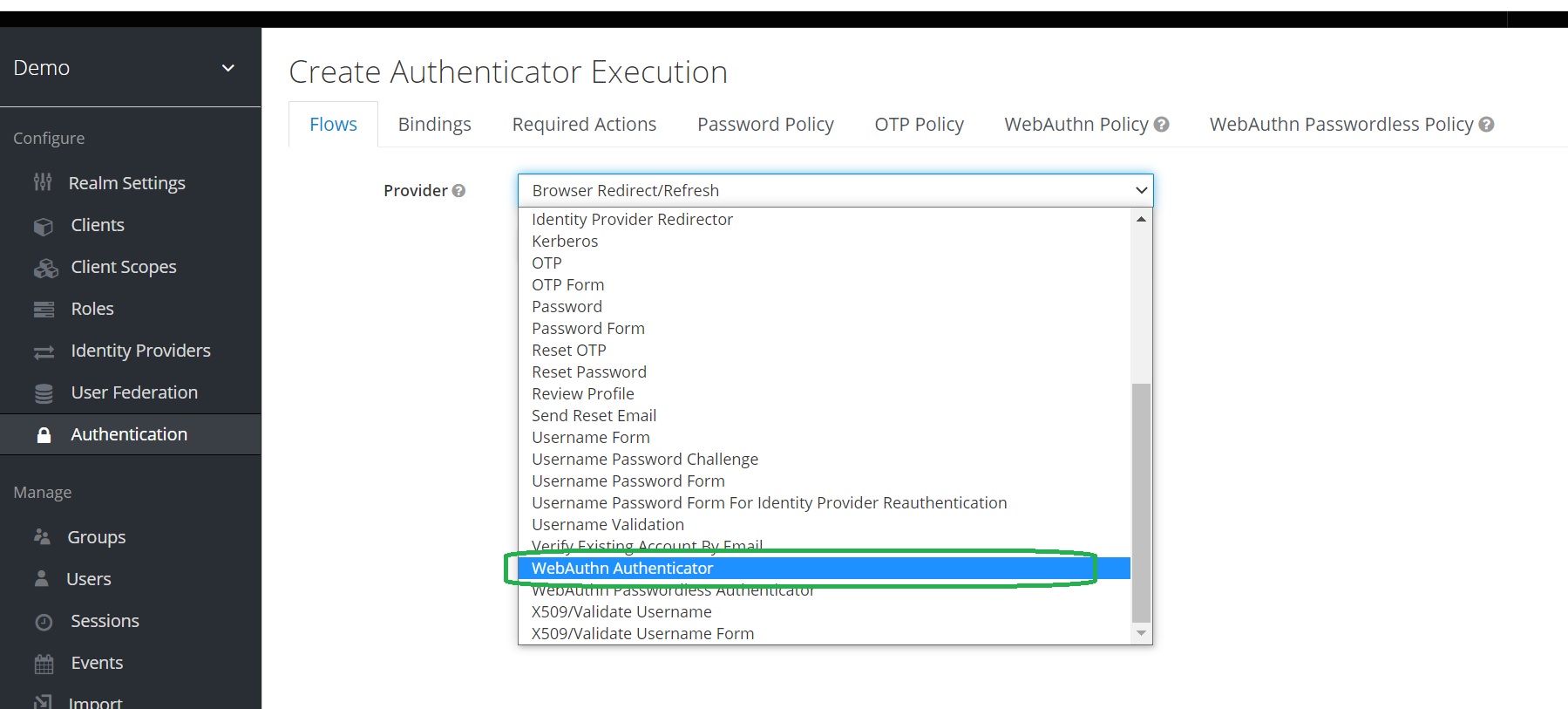
Two-Factor Authentication with Keycloak WebAuth · Ultimate Security Professional Blog
Types of two-factor authentication, pros and cons: SMS, authenticator apps, YubiKey

Two-Factor Authentication HackerOne Platform Documentation
Types of two-factor authentication, pros and cons: SMS, authenticator apps, YubiKey

Two-factor authentication explained: How to choose the right level of security for every account
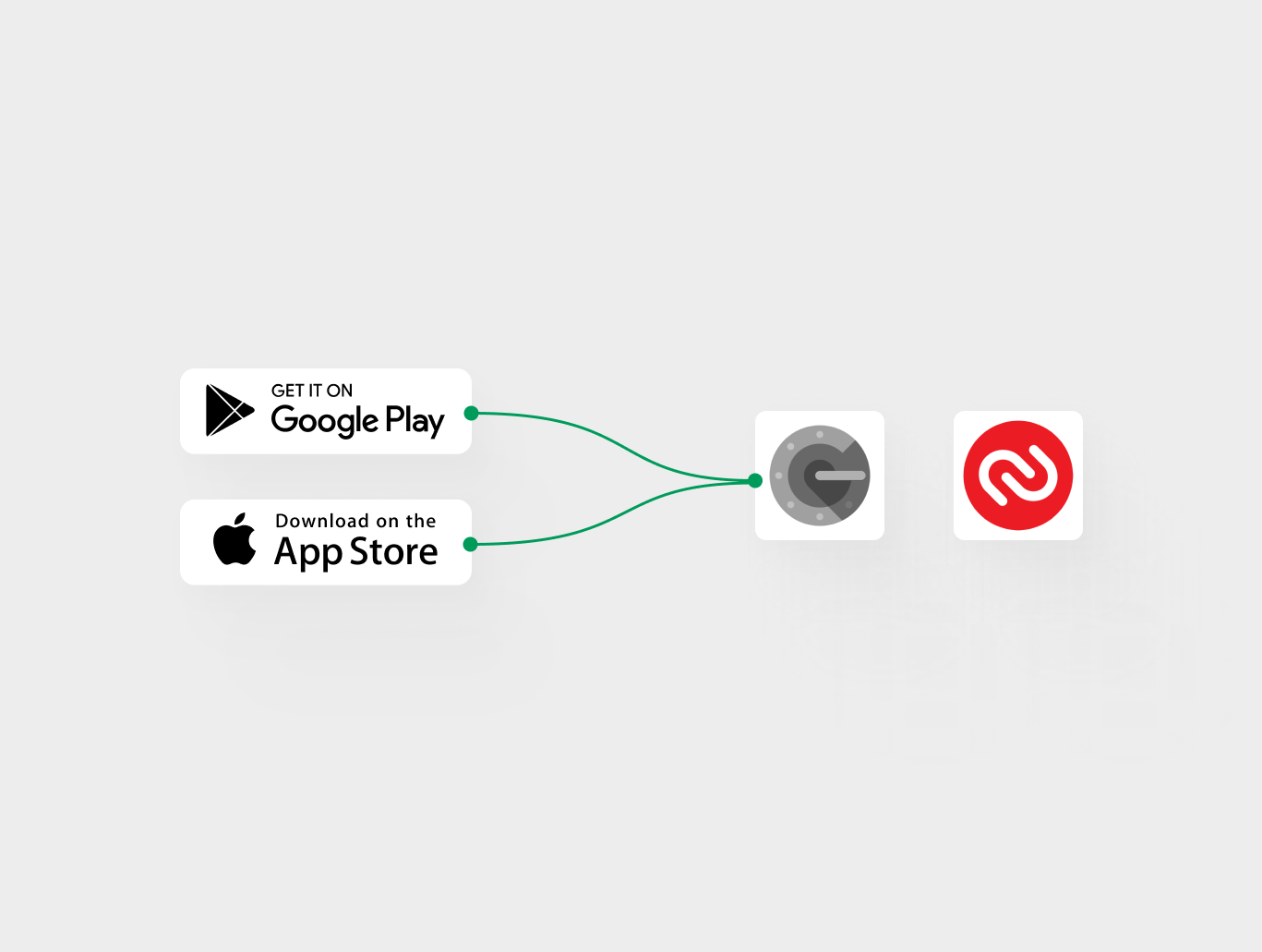
Step-by-Step guide: Setting up Two-Factor Authentication (2FA)
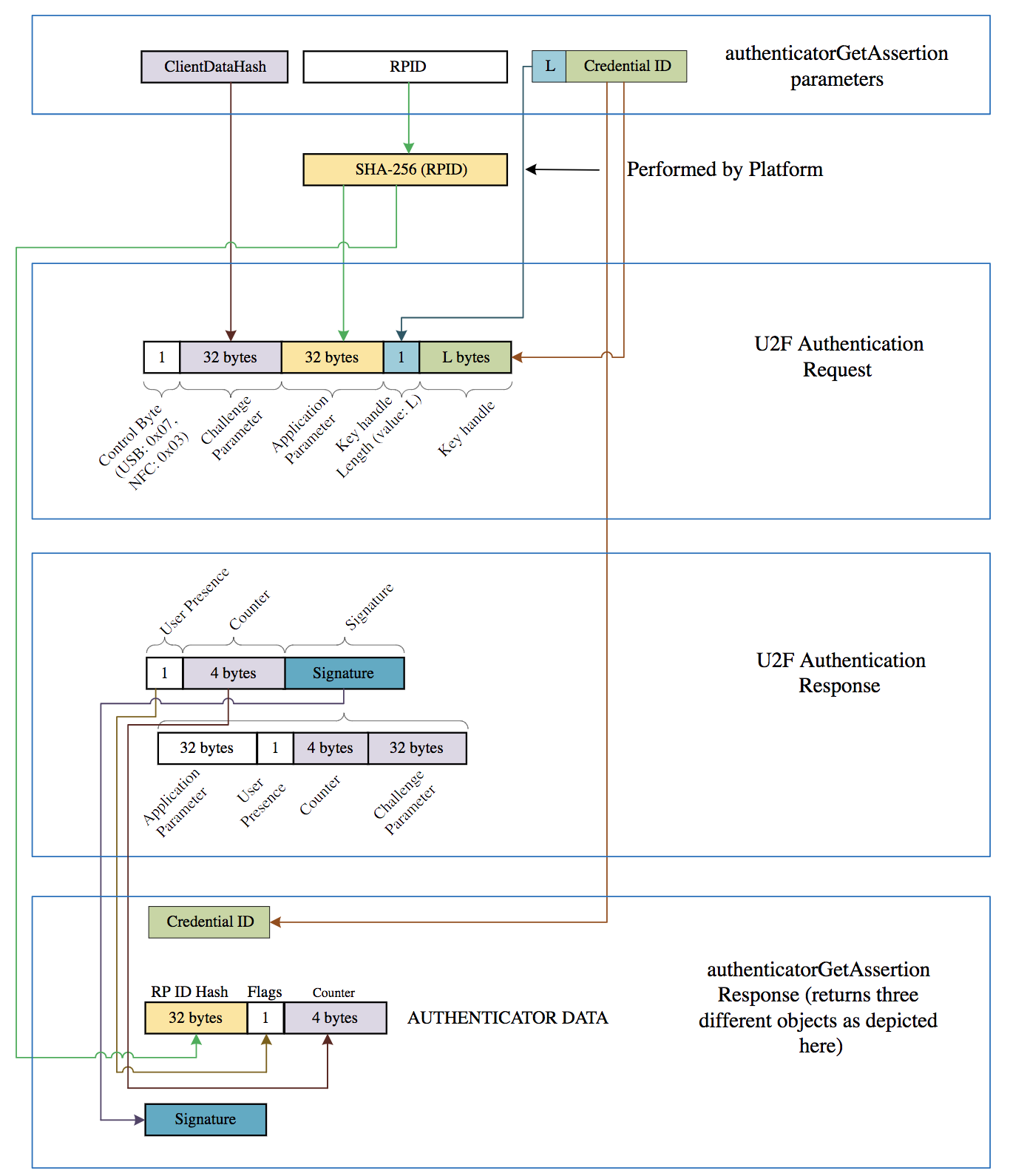
Client to Authenticator Protocol (CTAP)

Two Factor Authentication Explained: Cracking the Code
Are There Any Noticeable Patterns in 2FA Codes? - Best Reviews
Authentification Guide — Two authenticators
- Best Price $ 1000.00. Good quality and value when compared to hfhealthcare.org similar items.
- Seller - 743+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

LOUIS VUITTON Utility Phone Sleeve Monogram Canvas Crossbody Bag Brown
Buy It Now 22d 18h -

Louis Vuitton Nanogram Gold Tone Cuff Bracelet S Louis Vuitton
Buy It Now 10d 21h -

67 Louis Vuitton Archlight Sneakers ideas
Buy It Now 25d 10h -

Louis Vuitton Cologne Perfumes Collection Welcomes California Dream
Buy It Now 18d 19h -
:max_bytes(150000):strip_icc()/081922-designer-bag-trends-social-2000-11c5945491cf42e48b811a772de33e18.jpg)
These Are the 3 Biggest Bag Trends of 2022 Worth Investing In
Buy It Now 7d 17h -
![GUIDE] Louis Vuitton Neverfull Fake vs Real (50 Examples) – Bagaholic](https://cdn.shopify.com/s/files/1/0003/3492/1742/files/19_5fd52899-1339-4402-9fce-921fafe31845.jpg?v=1604496135)
GUIDE] Louis Vuitton Neverfull Fake vs Real (50 Examples) – Bagaholic
Buy It Now 18d 17h -
![HERMES] Hermes Vespa PM Vo Epson Blue Jean Light Blue/Silver Bracket – KYOTO NISHIKINO](https://shop-nishikino7.com/cdn/shop/products/I171823165-20_2f7fc4ba-c783-4da0-a376-8ed5e3220edd_800x.jpg?v=1698464779)
HERMES] Hermes Vespa PM Vo Epson Blue Jean Light Blue/Silver Bracket – KYOTO NISHIKINO
Buy It Now 8d 22h -

LOUIS VUITTON Monogram Neverfull GM 1312314
Buy It Now 14d 19h -
Gucci Women's GG1030SK Square Sunglasses
Buy It Now 20d 19h -

Art Print Poster / Canvas Louis Vuitton Effel Tower
Buy It Now 22d 19h -

Lv Speedy 25 Outfit
Buy It Now 27d 21h -

Camila Coelho - News, Photos & Videos on Camila Coelho
Buy It Now 18d 22h -

Ray-Ban Men's Outdoorsman RB3030-L0216-58 Gold Aviator Sunglasses
Buy It Now 9d 20h -

Authentic Louis Vuitton Black Epi Leather Keepall 55 Travel Duffle Bag – Paris Station Shop
Buy It Now 22d 23h -

Cate Blanchett Shines in Louis Vuitton Bow Dress at Cannes Festival – Footwear News
Buy It Now 10d 21h -

Louis Vuitton Briefcase Explorer Grey Monogram Eclipse
Buy It Now 13d 14h -

Fabric: Polyester Louis Vuitton Navy Blue Tracksuit, Size: Medium
Buy It Now 7d 22h -

Sleeping Beauty - Aurora Scene Loungefly Mini Backpack Bag OE 671803423411
Buy It Now 13d 23h -

Shoulder bags Etro - Pegaso canvas shoulder bag - 192P1N0418747150
Buy It Now 21d 12h -

Hermès Vintage - Epsom Kelly Belt - Grey Gold - Leather Belt - Luxury High Quality - Avvenice
Buy It Now 3d 11h -

Leather Handle Wrap
Buy It Now 21d 20h -

Soft LV Leather Back Case Cover For Iphone 12 Pro – Casecart India
Buy It Now 14d 5h -
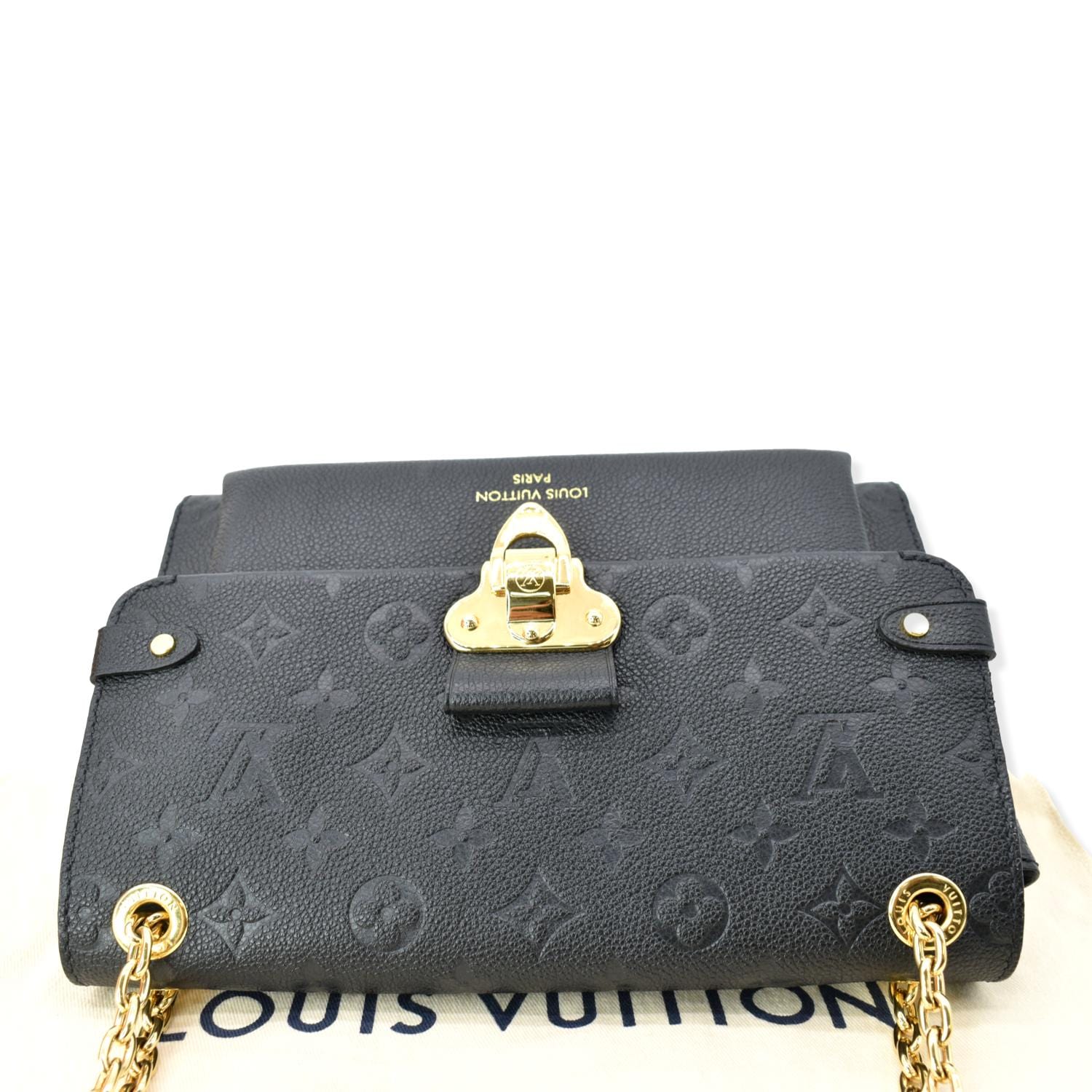
LOUIS VUITTON Vavin PM Monogram Empreinte Shoulder Bag Black
Buy It Now 26d 20h -

LOUIS VUITTON SHOES PALM BEACH PUMPS 37.5 features a damier ebene
Buy It Now 25d 16h