Perfect stack: A step-by-step guide to layering bracelets — Covet & Acquire
$ 70.50 Buy It Nowor Best Offer, FREE Shipping, 30-Day Returns

The Ultimate Guide to Creating the Perfect Bracelet Stack
startup-analysis/data/funding.csv at master · kyang01/startup-analysis · GitHub
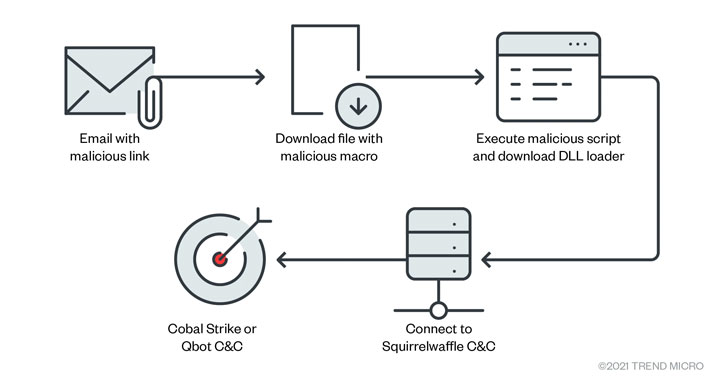
Hackers Exploiting ProxyLogon and ProxyShell Flaws in Spam C - vulnerability database

The Ultimate Guide to Creating the Perfect Bracelet Stack
ML2018SPRING/hw5/word2idx.json at master · voidism/ML2018SPRING · GitHub
Lunr.js Static Site Search Example

Remote Code Execution (RCE) - vulnerability database
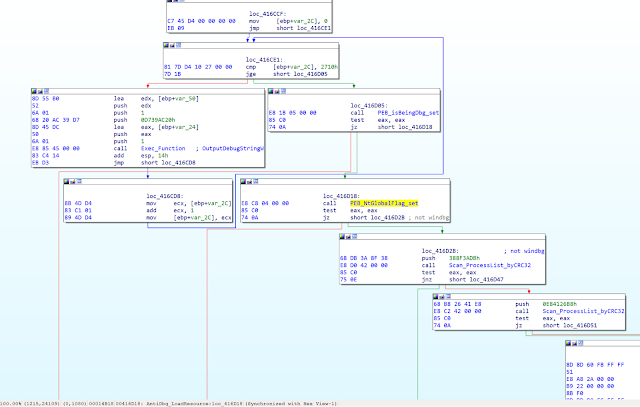
RATs and stealers rush through “Heaven's Gate” with new load - vulnerability database
RATs and stealers rush through “Heaven's Gate” with new load - vulnerability database
Perfect stack: A step-by-step guide to layering bracelets — Covet & Acquire
- Best Price $ 70.50. Good quality and value when compared to hfhealthcare.org similar items.
- Seller - 483+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-
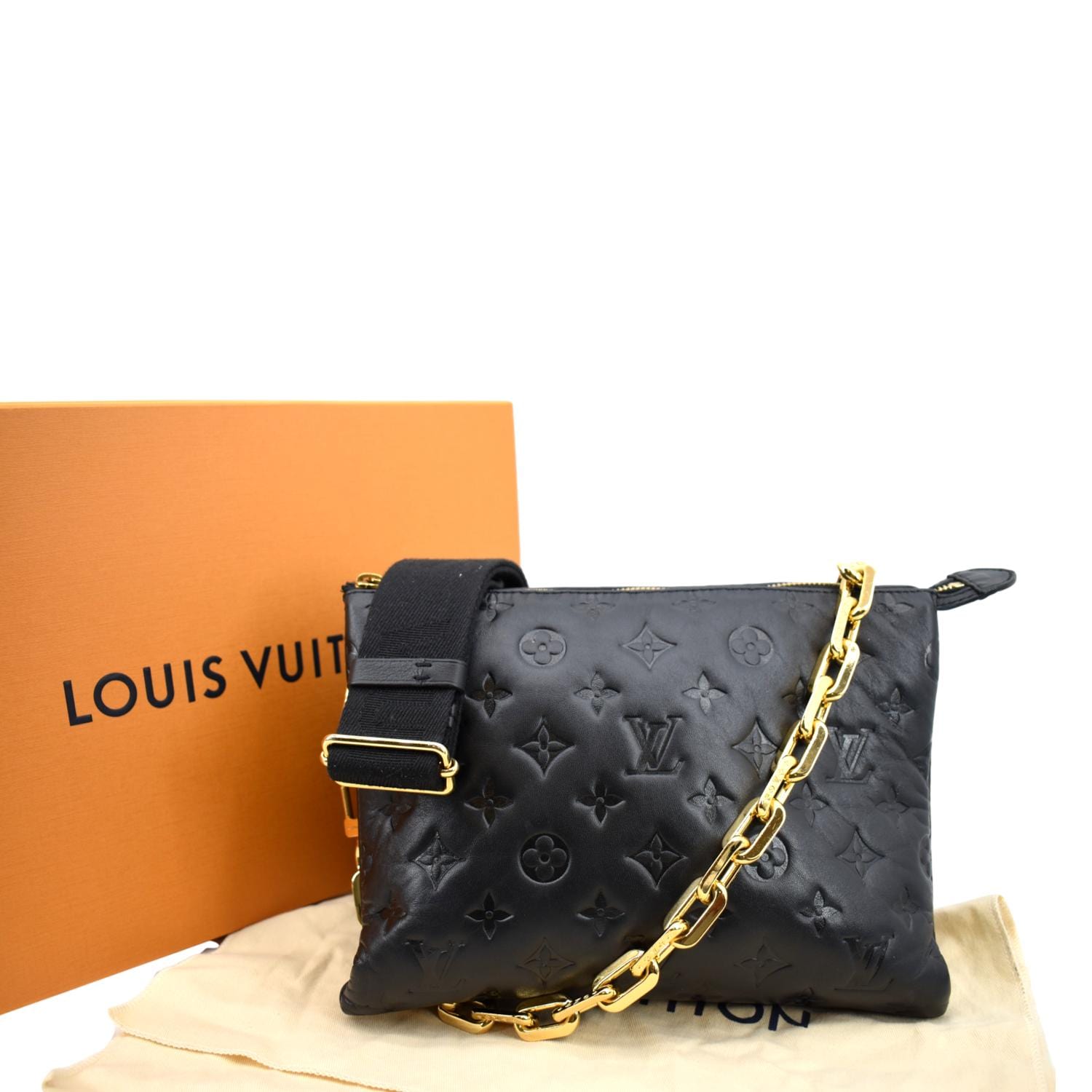
Louis Vuitton Coussin PM Monogram Embossed Shoulder Bag
Buy It Now 24d 23h -

Louis Vuitton Monogram Neverfull MM Tote Bag (hot pink interior) SD229 – KimmieBBags LLC
Buy It Now 4d 18h -

LOUIS VUITTON Empreinte Card Holder Black 1247758
Buy It Now 22d 19h -

Louis Vuitton Monogram Vernis Wilshire Tote mm
Buy It Now 4d 19h -

Women's Designer Bags & Purses - Luxury Handbags
Buy It Now 9d 12h -

LOUIS VUITTON Monogram New Wave Multi Pochette Accessories Shoulder St - MyDesignerly
Buy It Now 6d 8h -

Louis Vuitton Multi Pochette Accessoires
Buy It Now 24d 15h -

LC Lauren Conrad, Bags, Lc Lauren Conrad Candide Crossbody Bag White Floral
Buy It Now 17d 5h -

Hermès Limited edition Garden Party 36 - shop online
Buy It Now 25d 22h -

Christian Louboutin Loubila Denim Clutch in Blue
Buy It Now 15d 5h -

Margot New York Crossbody Bag Purse Brown Leather - Same Day Shipping!
Buy It Now 6d 19h -

Alexander Mcqueen shoes for Men
Buy It Now 2d 17h -

size 10.5 Bape X Checkerboard Old Skool Vans custom design for
Buy It Now 19d 9h -

Louis Vuitton Men's Cream Cashmere Cotton LV Rainbow Intarsia T-Shirt – Luxuria & Co.
Buy It Now 19d 23h -

Picotin 22 Insert - UK
Buy It Now 27d 9h -

Valentino Stud lock small shoulder bag Leather shoulder bag, Bags, Small shoulder bag
Buy It Now 9d 18h -

Louis Vuitton Kendall Travel bag 323893
Buy It Now 25d 8h -
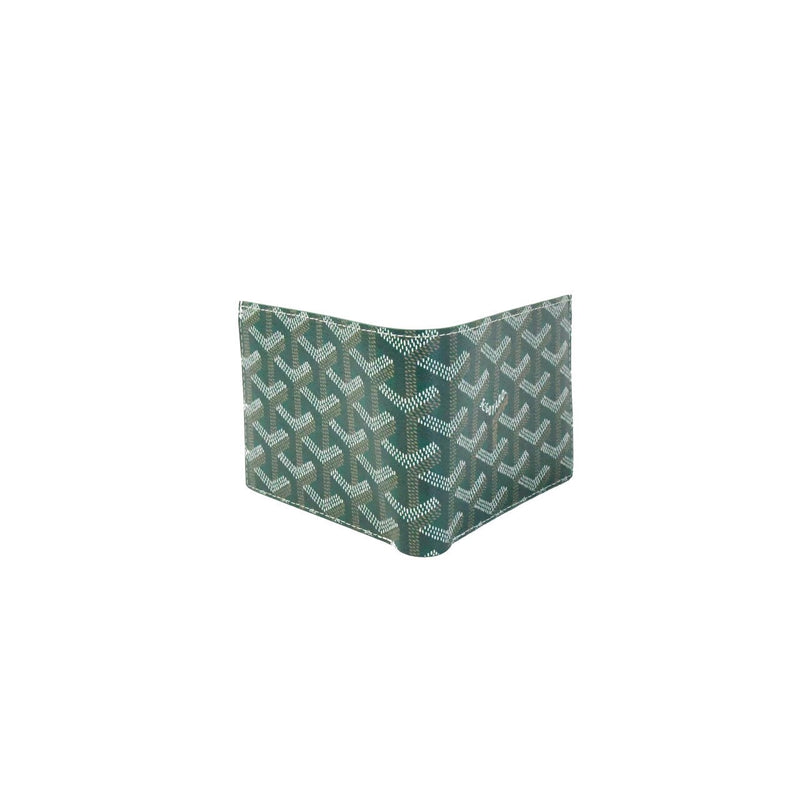
Goyard Bi Fold Wallet Green - NOBLEMARS
Buy It Now 11d 10h -

Designer Sunglasses for Women - Luxury Sunglasses - LOUIS VUITTON
Buy It Now 22d 16h -

Homepage Louis vuitton phone case, Iphone cases, Luxury iphone cases
Buy It Now 16d 23h -

Louis Vuitton Keepall Light Up LED Monogram
Buy It Now 18d 10h -
Robyn's Nest Custom Crochet
Buy It Now 9d 15h -

Bag Louis Vuitton Blue in Plastic - 30333793
Buy It Now 4d 13h -

A Beginner's Guide To Investing In Vintage Louis Vuitton Handbags
Buy It Now 8d 14h

